Our design is broken up into several components. After solving each component individually, they were pieced together to form a complete system.
As the primary display for the client machine, the television is an integral part of the voting machine. The display is text only the code driving it was optimized for such a purpose.
Card readerThe card reader used is a standard track two reader. For most cards, track two stores data that is easily accessible via other means (i.e. credit card numbers, student ID number, driver’s license number). When a user swipes their card, the machine will authenticate the number as valid (in our case, a valid Cornell ID) and allow the person to continue. If the card is not of the proper format, an error is returned. For our purposes, the student ID number is sufficient for authentication.
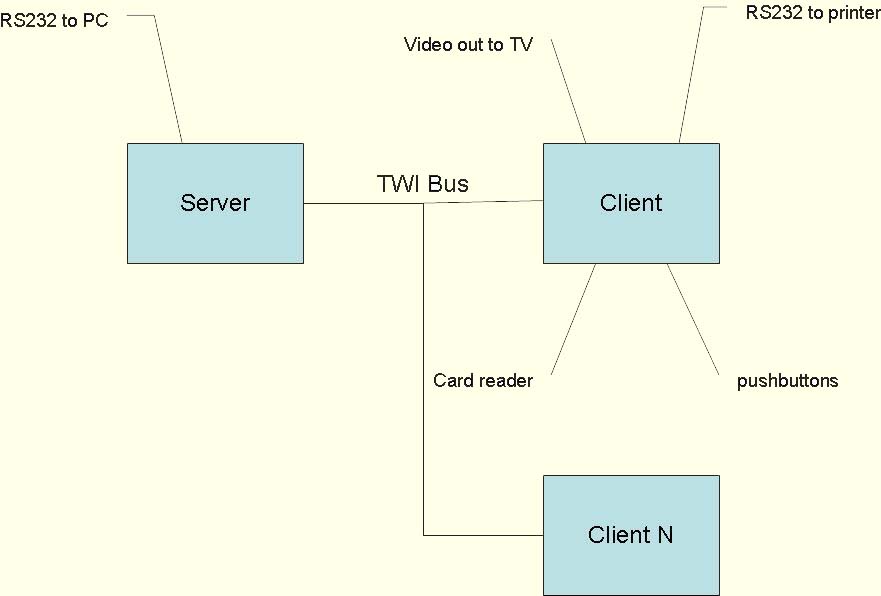
Communication between multiple chips via TWISince we planned on allowing multiple devices to simultaneously connect to one server, we needed to use some sort of common bus. Fortunately, the Mega32 has such a feature in the form of the Two Wire Interface. As the name implies, the TWI has two wires; one for a clock pulse and another for data. Since there can be multiple devices on the bus, the TWI also uses device addressing and a master/slave system to determine which devices are allowed to “talk” at any given time. By implementing some more robust communication protocols, data can be sent from the client to the server for verification and an acknowledgement can be sent from the server to the client.
PrinterSince digital data can be compromised and altered, we decided to implement a method to create a hard copy of a user’s selection. After a person has finished entering his or her choices and the data is verified, the text is sent out to the printer attached to the machine. After some experimentation, we discovered this was fairly simple to do, since it only required feeding the data through the serial port, followed by a form feed to start the printer.
The inherent tradeoff in this architecture is that the server requires more storage and processing power to be able to fulfill all client requests. This also creates a vulnerability in the system since it is a key component. A server compromise would be disastrous. However, coding a verification transaction protocol becomes much simpler in a client/server architecture. An alternative would be a peer to peer system. In this method, a machine must communicate with every other machine on each transaction. Furthermore if any of the client machines where to go down, they will not be able to respond to requests. A client/server architecture is advantageous in this scenario as it simplifies programming and makes the system easier to control.
TV outputSince the output was simple text, an LCD screen may have been sufficient to provide the same level of information as a TV screen. Since the TV screens are not considered part of the budget, they were chosen over the somewhat expensive LCD screens. As a tradeoff, a more complex (and more expensive) chip was required. In addition, the Mega32 provided us with functionality in serial interfaces that would be used for I/O simplifying our code.
Printer InterfaceTo print, we elected to use a serial interface. This is relatively low tech and easy to implement since almost every printer has the ability to take ASCII characters as input. The ability to use newer and more feature rich printers would require the use of postscript. This would allow for graphics and nicer looking text since printing is based on a language which describes a series of geometric shapes and intensity. As a result of simple printing, the paper ballots are easily reproducible, and more complex hardware would have been needed to provide more protection.
Secure MCUAtmel has a series of secure microcontrollers. These micocontrollers are much more expensive than the regular AVR class. These microcontrollers have dedicated hardware to prefrom cryptographic operations in parallel to normal program execution. In addition is provides two operations of user and super user modes, to protect accesses to memory. It can self monitor external voltage and frequency to detect tampering, this chip is much more reallible and secure for such a task. Since we used simple logic we had to attempt to include this type reliability in hardware.
Stripes on the magnetic cards normally use the same format as bank or financial cards, (ISO 7811). We only use track two which contains up to 40 bits of numeric data. A number is represented as a 5 bit number, the least significant bit transmitted first then followed by an odd parity bit. A sequence of zeros are transmitted from the reader, to help with alignment then the first character is sentinel character signifying the start of the sequence. Next the data and finally a end sequence character with one last numerical data. This last character of data serves as a longitudinal redundancy check. It contains the bit sum of each previously transmitted character. Using this information means at least 4 errors must exists before an invalid card can be read as valid.
ASCIIAmerican Standard Code for Information Interchange what used to represent alphanumeric characters and symbol on both the TV screen and the printer. Ascii is character set that uses 7 bits to represent most symbols, and is commonly in use today. Other possible implementations included the ascii extended and ansi charcterset.
EACThe America vote act legislation passed in 2002 provided a set of voluntary voting guidelines to be implemented by the Federal Election Commissions (FEC) and the election assistance commission (EAC). These guidelines address every type of voting system including electronic voting, known as Direct Recording Electronic. Listing the requirements of the machines with users and interfaces, allong with testign guidelines. The full 200 page report is available at EAC.